
You can find it tricky to remove Counter.wmail-service.com from your PC if you are not familiar with technical stuff. The user has to uninstall all related items in the Control Panel, Registry, and System files to completely remove the malware. If you are not confident in doing this, the easiest way is to use a good anti-malware tool. The tool will scan your system and remove the Counter.wmail-service.com automatically. Furthermore, take measures to keep your operating system and Software up-to-date. Make sure to keep an eye out for suspicious emails or downloads from unknown sources.
You may wonder why you have to remove so many files from your computer for Counter.wmail-service.com. It is a Command & Control server that controls VenomSoftX, a harmful malware. VenomSoftX is a sneaky software that is JavaScript based. It can secretly take control of your computer remotely without you knowing.
This dangerous malware can steal your cryptocurrency and other digital information on your PC. If you don’t remove all its associated files, it will keep hiding on the computer and keep appearing. So it’s essential to protect your computer from such malware using strong security measures and browsing the internet cautiously. Read on to learn some easy methods to remove malware-affected files on your PC.
Easy ways to get rid of malicious applications on your PC
As a JavaScript-based RAT or remote access trojan horse, Counter.wmail-service.com is quite a dangerous computer infection. If this malware type infects your device, you must remove it as soon as possible. These Trojans wreak havoc inside your PC, which is why they are dangerous.
Counter.wmail-service.com is responsible for more than 70% of the malware attacks. Hence, it is a serious threat to your computer device. Make sure to regularly update your antivirus software and operating system. Since it’s better to prevent than repair, using anti-malware will defend your device against malware.
Threat information
| Threat Name | Counter.wmail-service.com |
| Malware Type | Command & Control (C&C) for VenomSoftX RAT |
| Malware Effect | This Trojan is designed to steal cryptocurrencies and hijack other sensitive digital information. |
| Threat Level | High |
| Threat Symptoms | System crashes and freezes, slow PC performance, and error messages. |
| Threat Source | Third-party website apps, ads on suspicious websites, fake mail |
| Threat removal method | Remove all related files and install anti-malware tools. |
Threat analysis of Counter.wmail-service.com
As you know from above, Counter.wmail-service.com can cause serious harm to your computer. Although it’s a relatively new malware, it works to carry out various malicious activities. Its main purpose is to steal important information from your device. Then use it to extract money from you in different ways. It can also allow cyber criminals to remotely control your computer to perform illegal tasks.
Moreover, Counter.wmail-service.com can also spy on you through your device camera, microphone, and other methods. The malware program can also record your actions and follow your keystrokes on the keyboard when you type sensitive data. Additionally, this Trojan can turn the device into part of a botnet, which means the device can be used to attack other computers through a network. Malicious Software can also mine cryptocurrencies and put a heavy load on your system that leads to crashes.
It’s important to remove Counter.wmail-service.com from your computer as soon as possible. Use reliable antivirus software to scan and eliminate the threat. Keep your Software and operating system up-to-date to minimize vulnerabilities. Moreover, be cautious with suspicious emails or downloads, and avoid clicking on unknown links on the browser. Take all these precautions to avoid this risky Trojan or other similar malware hiding in your PC.
How does the Counter.wmail-service.com Trojan harm the computer?
When there is a Counter.wmail-service.com malware attack, it can cause severe damage. Here are some major harmful effects of this malware:
-
Remote Access and controlling device
The Counter.wmail-service.com is a JavaScript-based RAT that allows the attackers to gain unauthorized Access to the victim’s computer remotely. Moreover, the attacker can manipulate files, steal sensitive information, or even take over the entire system. This privacy loss can result in big financial loss, identity theft, or even corporate spying.
-
Cryptocurrency Hijacking
The malware’s primary goal is cryptocurrency hijacking. So, when it comes inside the system, it can access cryptocurrency wallets to steal private keys. It can also directly manipulate the transactions. It can cause the loss of valuable digital assets, leaving victims financially destroyed.
-
Data theft and information breach
The infection of Counter.wmail-service.com allows attackers to get personal and sensitive data from the infected computer. The data may include login credentials, personal files, financial information, and browsing history. Furthermore, they can use the data for identity theft, sell them on the dark web or hold them for ransom, causing harm to the victim’s privacy and reputation.
-
Unstable system performance
VenomSoftX malware infections can consume a considerable amount of system resources, causing performance degradation and system instability. Moreover, the infected computer may experience slow response times. Frequent crashes and unknown errors that disturbs normal operation and loss of productivity.
-
Infection propagation
Since Counter.wmail-service.com is a Command & Control server, it can control multiple infected devices at once. When an endpoint is infected, the malware can spread through the network, infecting other devices in the same network. Due to this propagation capability, the infection can lead to a widespread outbreak within an organization or a community. This can cause massive operational or financial loss.
Hence, Counter.wmail-service.com is a dangerous threat to security and privacy on an individual level and a mass level. It does not stop at stealing data but controls devices to spread infection and launch hostile attacks.
What happens when Counter.wmail-service.com starts a ransomware attack?
When Counter.wmail-service.com starts a ransomware attack, it will encrypt the victim’s data on their computer system. The ransomware program related to the server takes control of the critical files, so the user can’t access them. Its algorithm makes it nearly impossible for the victim to decrypt the files without the unique decryption key the attacker has.
Moreover, when the encryption process is complete, the victim will have a ransom note. The ransom note usually pops up as a message or text file on the desktop. The note will have instructions on how to pay the ransom. It typically involves cryptocurrency and asking for a decryption key, and regaining Access to the fines. Moreover, the attack will have severe consequences like data loss, financial loss, and disturbance in the victim’s personal and business operations.
How does your PC get attacked by the Counter.wmail-service.com virus?
There are various ways the Counter.wmail-service.com virus can come into your system. The infection mostly involves social engineering and exploiting vulnerabilities. Here is how your PC can get the Counter.wmail-service.com virus:
-
Malicious email attachments
One common method is through phishing emails that contain infected attachments. These emails trick the recipients into opening the attachments that execute Counter.wmail-service.com on their system. Moreover, the email may masquerade as a legit message from a known source to encourage the user to click on it.
-
Malicious Adware
Counter.wmail-service.com can come through malicious advertisements on the websites too. These ads may automatically download and install Counter.wmail-service.com when the user clicks on it. It can also infect without any interaction from the user.
-
Unsecure websites and downloads
When you visit an infected site or download files from untrusted sources, it can lead to infection. Attackers can inject Counter.wmail-service.com into legitimate websites or offer malicious files that mask as something harmless.
-
Exploiting software vulnerabilities
The malware can exploit security flaws in Software, such as outdated operating systems or unpatched applications. Once the attacker finds a vulnerability, Counter.wmail-service.com can get unauthorized Access to the system.
-
Drive-by Downloads
The drive-by downloads are the malware that gets installed on the user’s computer without their knowledge. It can happen through an exploit kit that scans for vulnerabilities and automatically activates the malware.
-
Social engineering techniques
Cybercriminals can use social engineering techniques like fake software updates, false alerts, or misleading messages. It tricks the users into downloading and installing the malware willingly.
-
Infected external devices
When you plug in an infected USB drive or other external devices, it can install malware into your system.
Use the guide to block notifications in browsers for Anti-malware action
Counter.wmail-service.com malware first asks for permission to enable the web browser notifications to install the Trojan. So start with the blocking process on your browsers before starting the manual removal process.
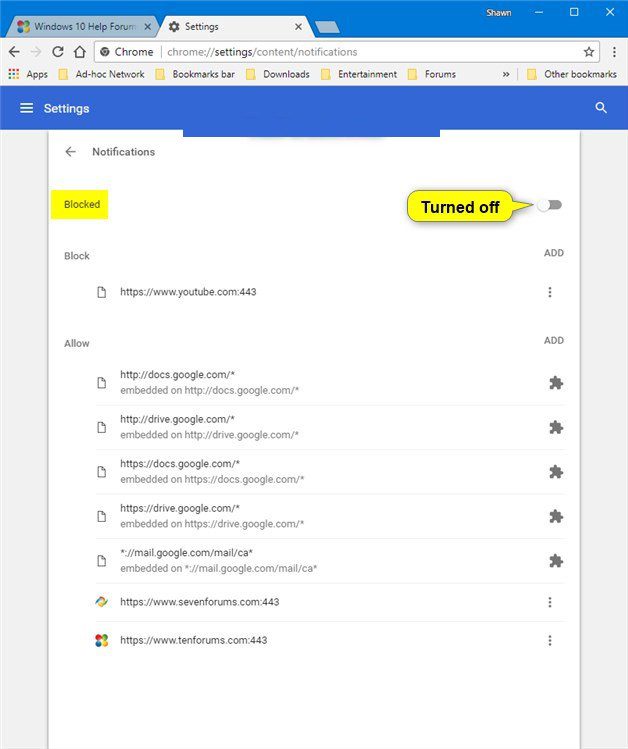
Google Chrome on PC
- Click on the three dots menu extension button in the upper right corner of Google Chrome.
- Go to “Settings,” then the “Privacy and Security” section and select “Content Settings,” and then the “Notification” option.
- Check for all suspicious URLs and block or remove them from the list by clicking on the right side of each URL.
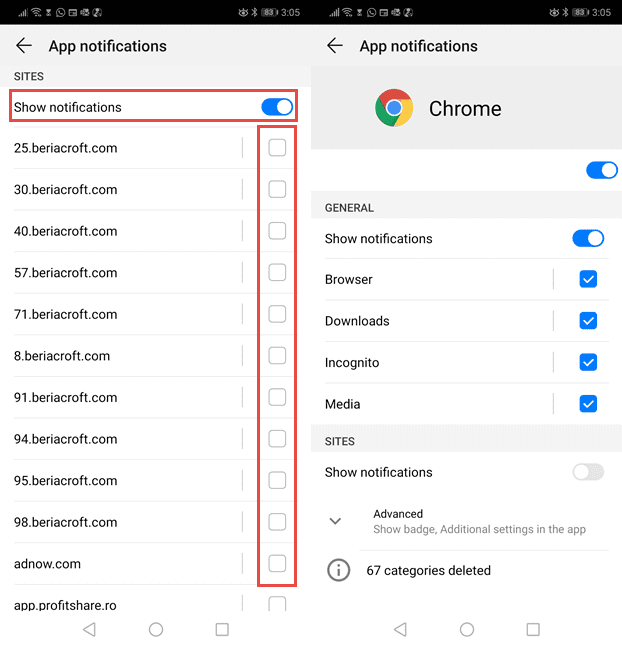
Google Chrome on Android
- Go to the “Settings” page on the browser clicking on its extensive menu button in the upper right corner of the screen.
- Now select the “Site Settings” option before clicking on the “Notifications” option.
- Select the very suspicious URL on the screen.
- Now select the “notification” and toggle “Off” in the permission section.
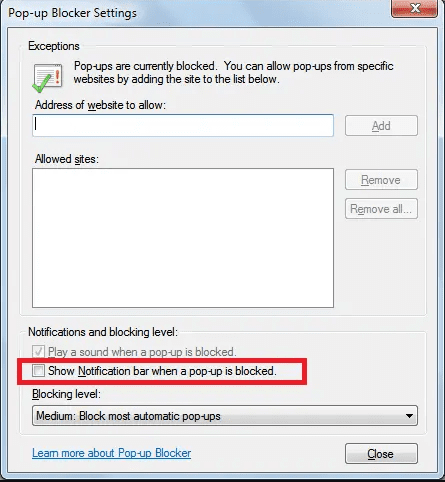
Internet Explorer
- Find the Setting button in the right corner of the Internet Explorer window.
- Go to the “Internet Options.”
- Select “Settings” from the “Pop-up Blocker” section under the “Privacy” menu.
- Select each of the suspicious URLs and click on the “Remove” option from the menu.
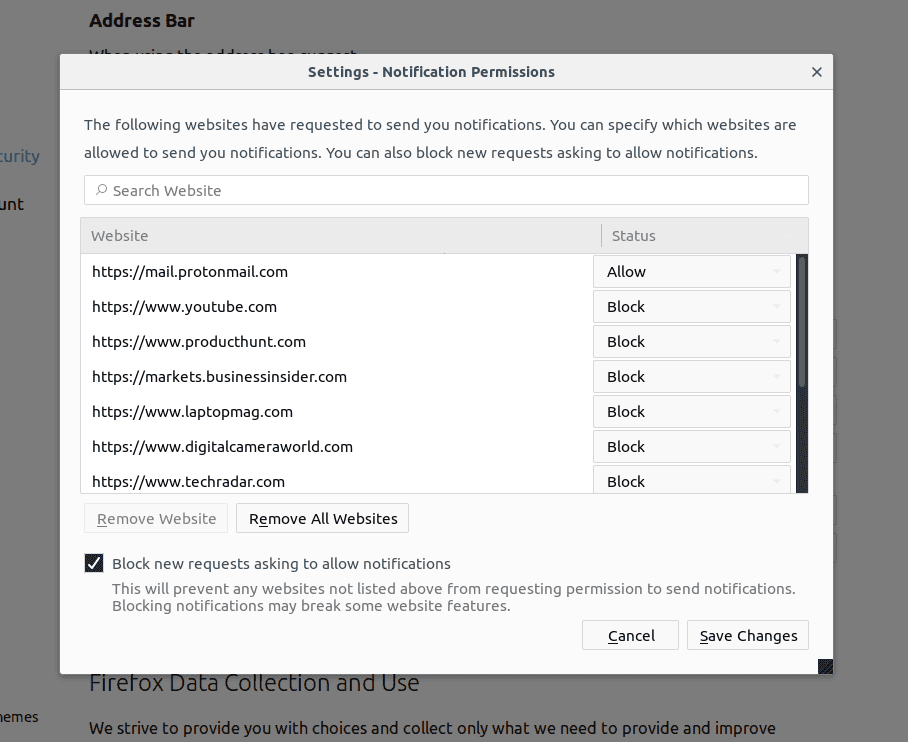
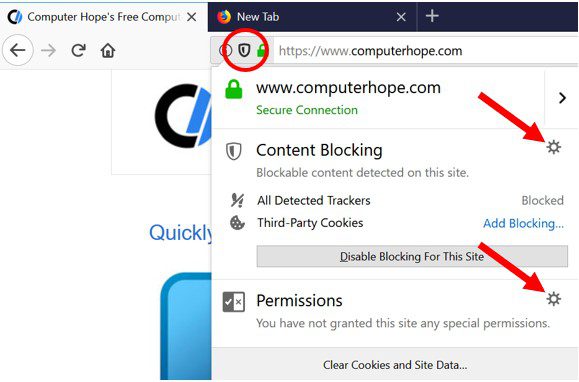
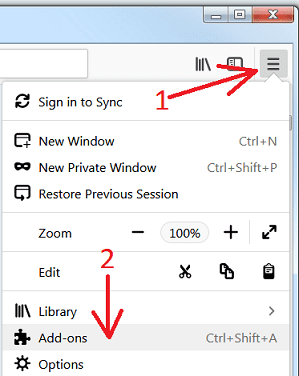
Mozilla Firefox
- At the top-right corner of your screen, find three dots representing the “Menu” button.
- Click on “Menu,” then choose “Options,” and go to “Privacy and Security” in the left-side toolbar.
- Scroll down to find the “Permission” section, then click on the “Settings” option next to the “Notifications” menu.
- A new window will open. Identify and select all the suspicious URLs.
- Now click on the drop-down menu and choose the “Block” option, so these URLs can show any notifications.
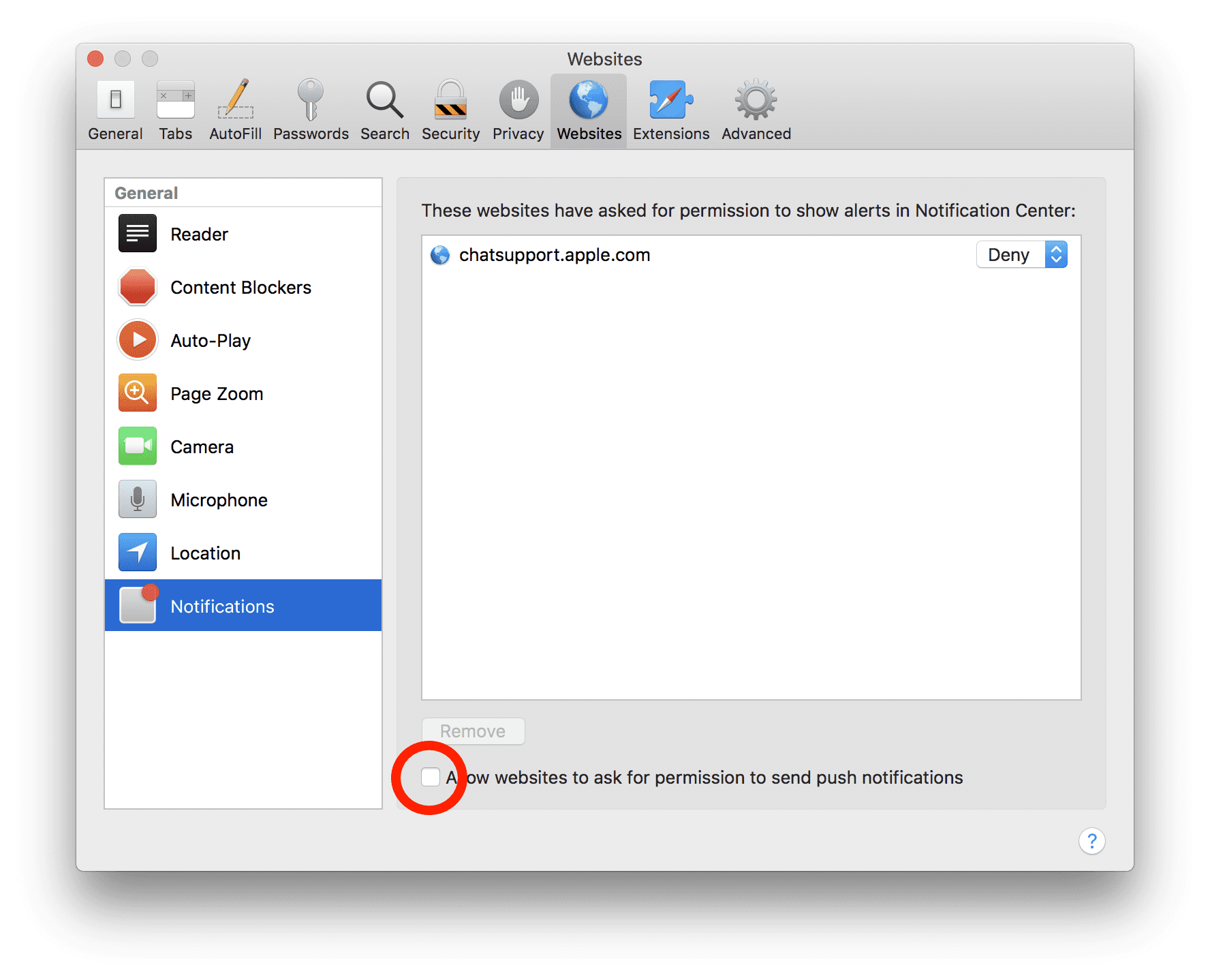
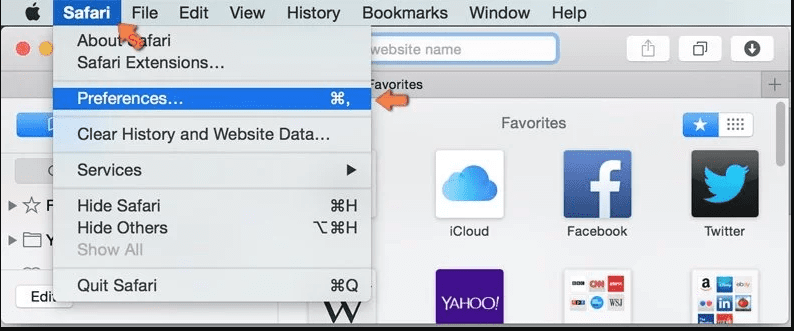
Safari in Mac
- Navigate to the upper right-hand corner and click on “Safari.” Select “Preferences” from the drop-down menu.
- Go to the “Website” tab and find the “Notification” section in the left panel.
- Look for the suspicious URLs and choose the “Deny” option to prevent notifications from them.
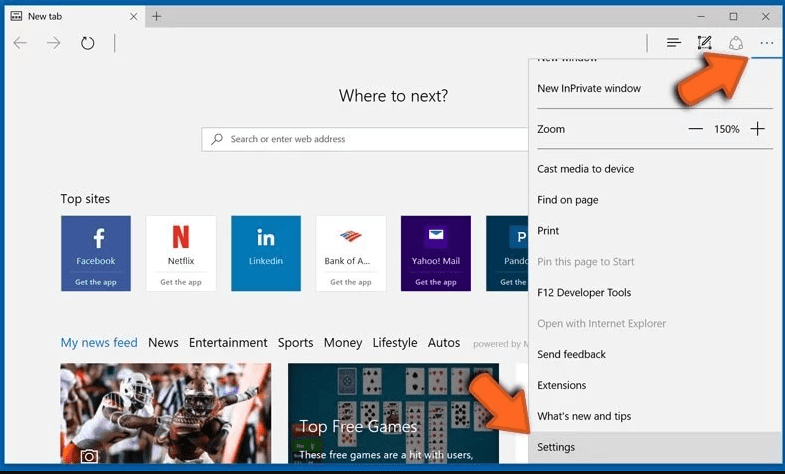
Microsoft Edge
- Launch Microsoft Edge and click on the three dots located in the top-right corner to access the menu.
- Select the “Setting” menu, then click on “View advanced settings.”
- Find the “Website Permissions” section and click on the “Manage” option.
- For each suspicious URL, toggle the switch to turn off permissions.
Removing Counter.wmail-service.com in the manual process:
- Uninstall all apps from Control Panel related to Counter.wmail-service.com
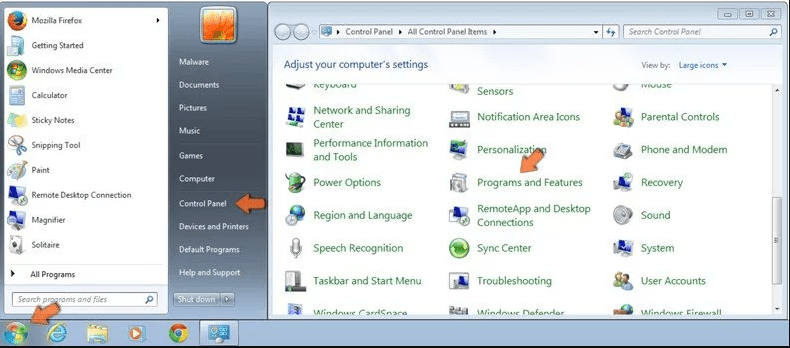
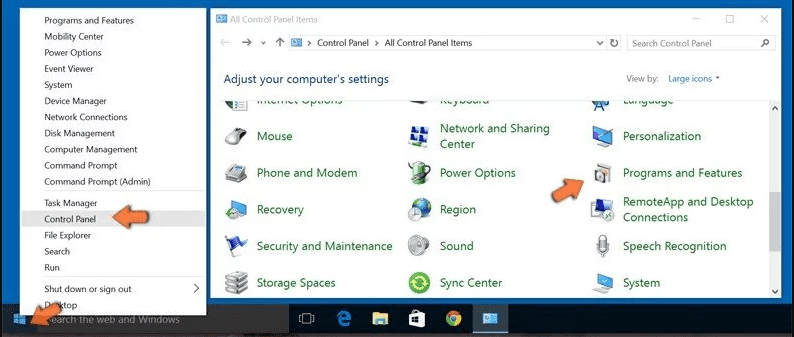
- In Windows 7, 10, and 8, Users
Click on the Start button shown as the Windows logo at the bottom-left corner of your desktop screen. Next, click on “Control Panel” from the options. Find the” Programs” section and click on “Uninstall Program” to proceed.
-
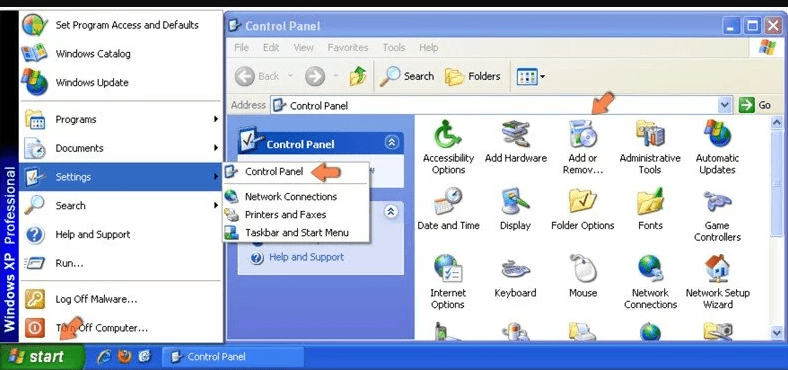
In Windows XP Users
Get started on Windows XP users by clicking on the “Start” button and then selecting “Settings.” Then click on “Control Panel.” Find the “Add or Remove Programs” option and click on it.
-
Windows 10 and 8 Users:
Go to the lower left corner of the screen and right-click. In the “Quick Access” menu, choose “Control Panel”. In the newly opened window, choose “Program and Features”
-
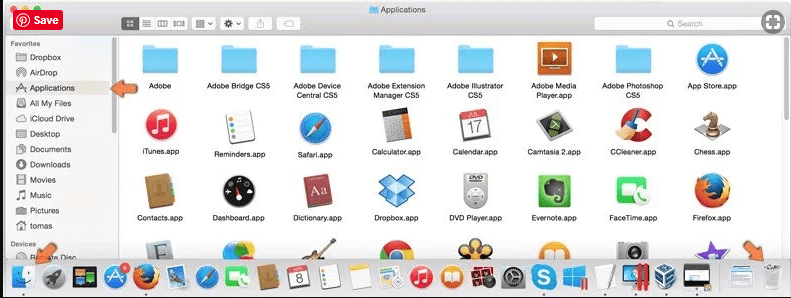
Mac OSX Users
Click on the “Finder” option. Then, select “Applications” on the screen. In the Application folder, just drag the app you want to remove to the “Trash” bin. Next, right-click on the Trash icon and choose “Empty Trash” to delete all the infected applications.
Removed all potentially unwanted programs responsible for Counter.wmail-service.com issues. Once everything is clear, use an anti-malware tool to scan your computer for any PUPs, PUAs, or any potential malware infections.
-
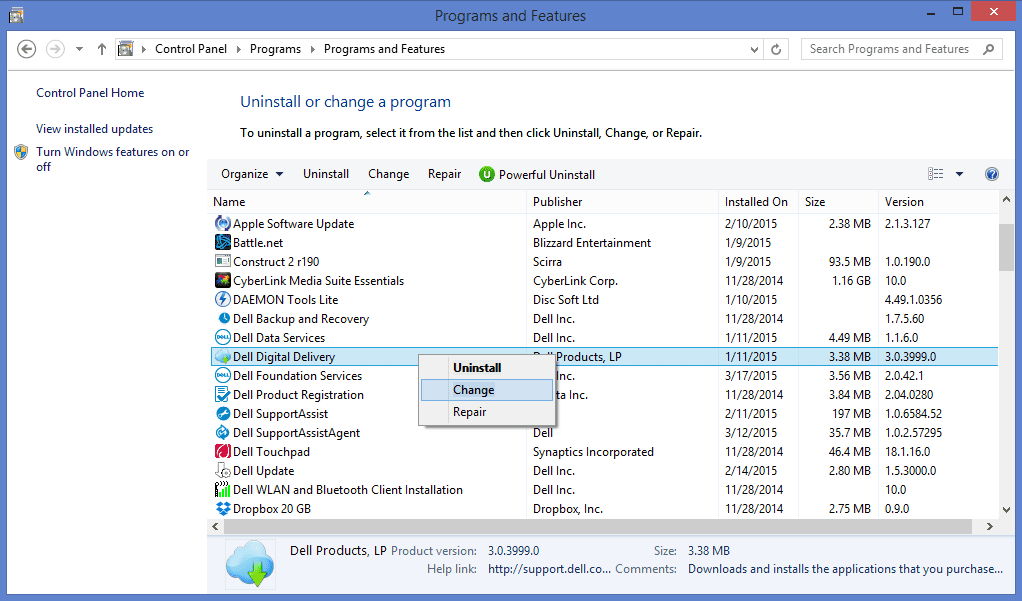
Delete malicious add-ons and extensions from Internet Explorer (IE)
Find the gear icon at the top-right corner of the Internet Explorer. Select “Manage Add-Ons” from the options. Look for any suspicious plug-ins or add-ons installed and click on the “Remove” option to uninstall them. If there are still the effects of Counter.wmail-service.com, reset the Internet Explorer settings to default in your system.
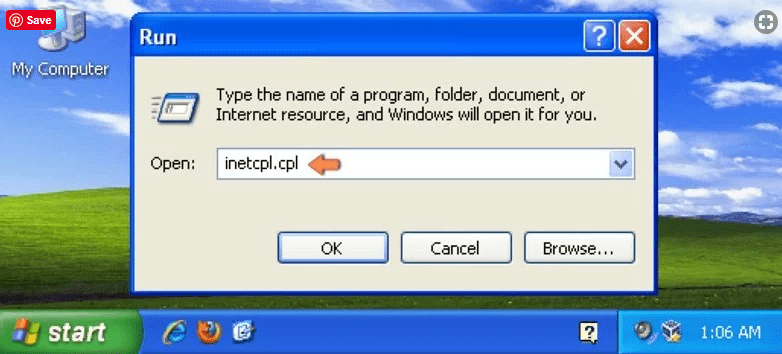
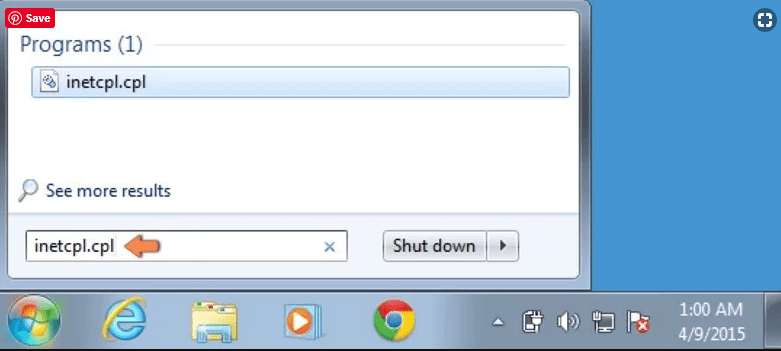
- Reset IE for Windows XP
Click on the “Start” button to start the process. Then select “Run.” A new window will open. Type “inetcpl.cpl” and click on the “Advanced” tab. Finally, press “Reset” to complete the process.
- Reset IE for Windows Vista and Windows 7
Click on the Windows logo in the bottom-left corner of the taskbar, and enter “inetcpl. cpl” in the start search box. Then click enter, and a new window will open. Click on the “Advanced Tab” and then select the “Reset” button.
- Reset IE for Windows 8
On Windows 8, open Internet Explorer and click on the “gear” icon. Next, click on “Internet Options.” A new window will open. Select the “Advanced” tab on it.
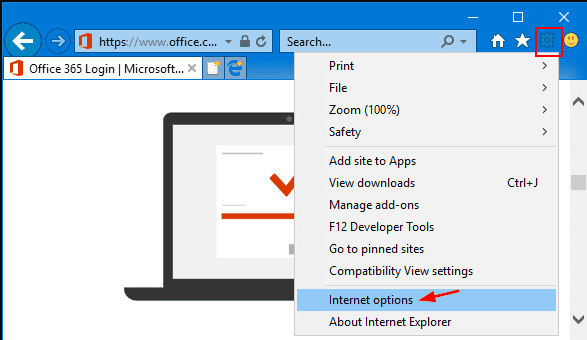
Then click on the “Reset” option.
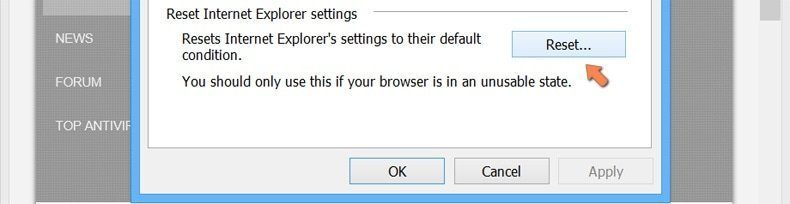
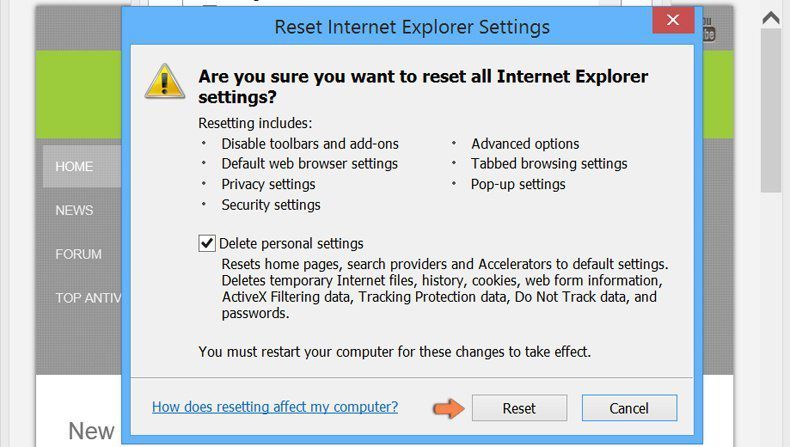
Again click on the “Reset” button to confirm you want to reset Internet Explorer.
- Remove Counter.wmail-service.com plug-ins from browsers
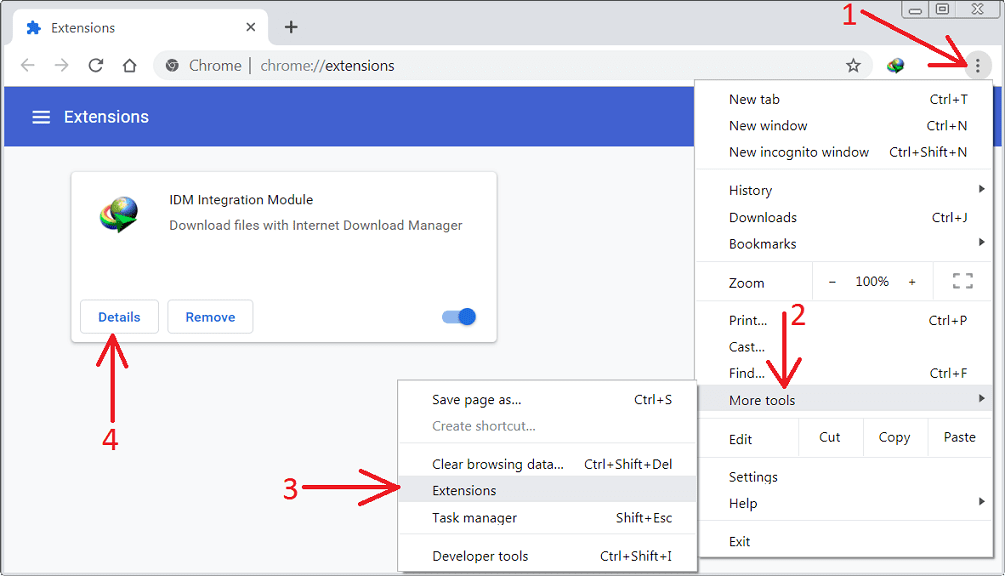
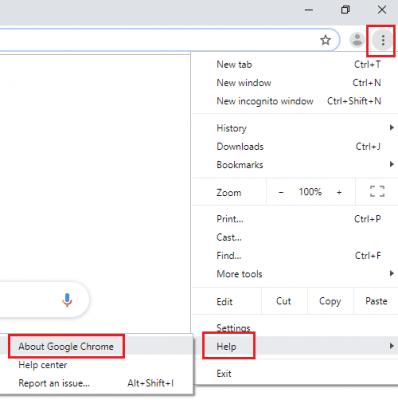
- Delete extensions from Google Chrome
Access the Google Chrome menu by clicking on the three vertical dots. Then choose the “More tools” option and then “Extension.” Find any installed add-ons and remove them all.
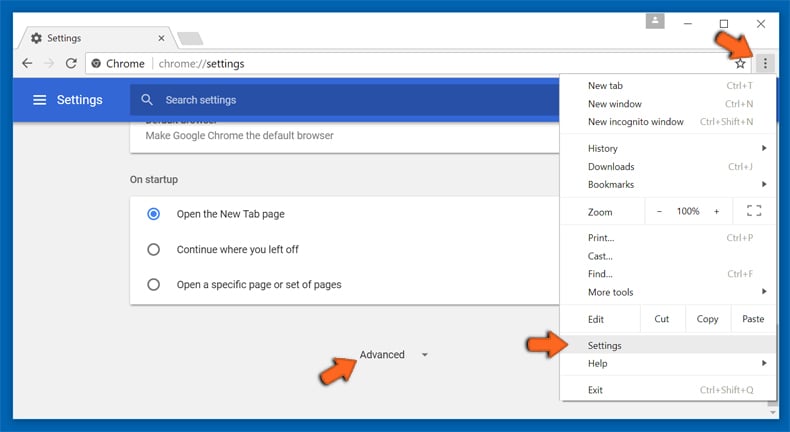
If you still face issues related to Counter.wmail-service.com, you can use another way to do it. It’s recommended to reset your Google Chrome browser settings. Go to “Settings,” then choose the “Advanced” option.
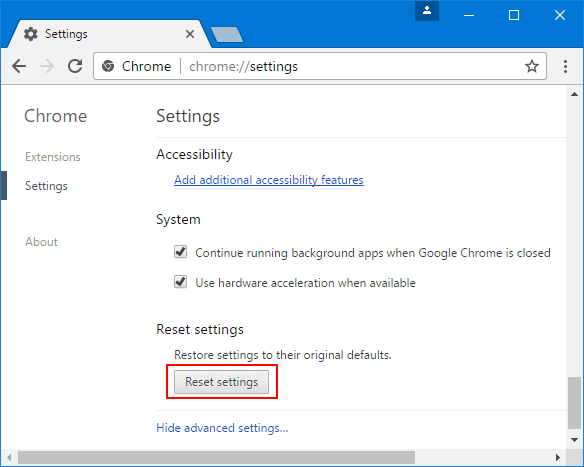
Next, click on the “Reset Settings” option.
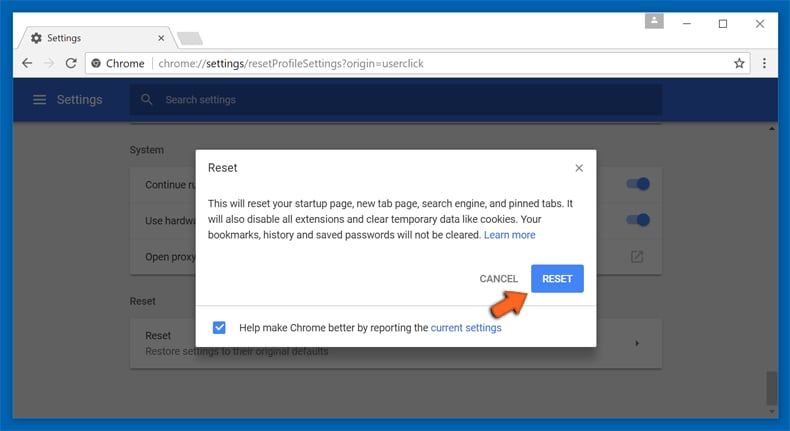
Now, confirm the “Reset” in the new window to run IE in its default setting.
- Remove extensions from Firefox Mozilla
Go to the Firefox menu to choose “Add-ons.” Click on “Extensions” and then select all the browser plug-ins to remove.
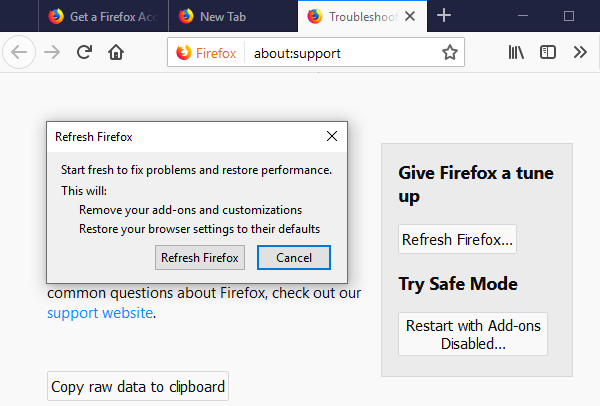
If you still face the issue, go to the extensive menu button. Then hover over “Help” and click on “About Google Chrome.”
Next, click on “Troubleshooting Information.”
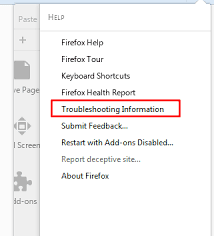
A new window will pop up. Click on the “Refresh Firefox” button. Then confirm your choice to run Firefox in Default.
- Remove suspicious extensions from Safari
In the browser, go to the “Safari” menu and select “Preferences.”
A new window will pop up. Click on the “Extension” category and select all the recently installed “Extensions,” and then click on “Uninstall.”
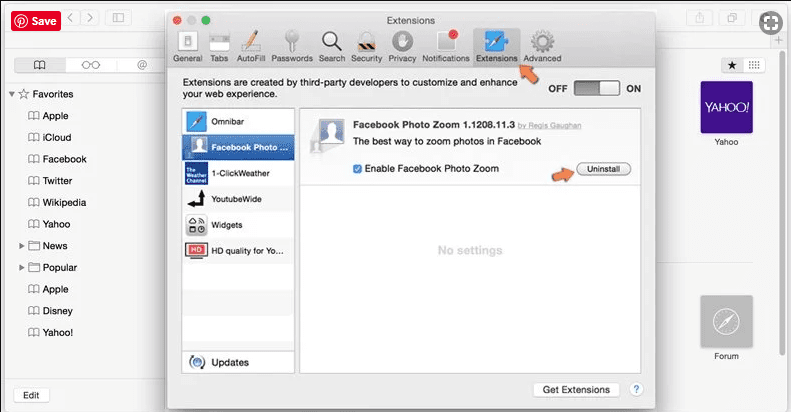
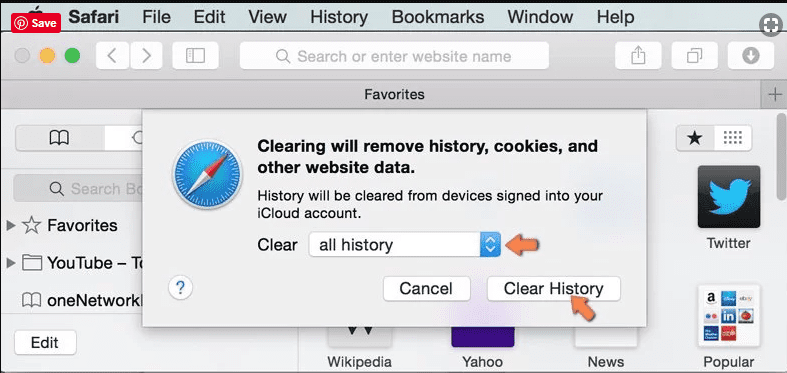
If the malware symptoms still occur, go to the Safari Menu, and select “Clear History and Website Data.” Select “All History” before confirming the “Clear History” menu on the pop-up window.
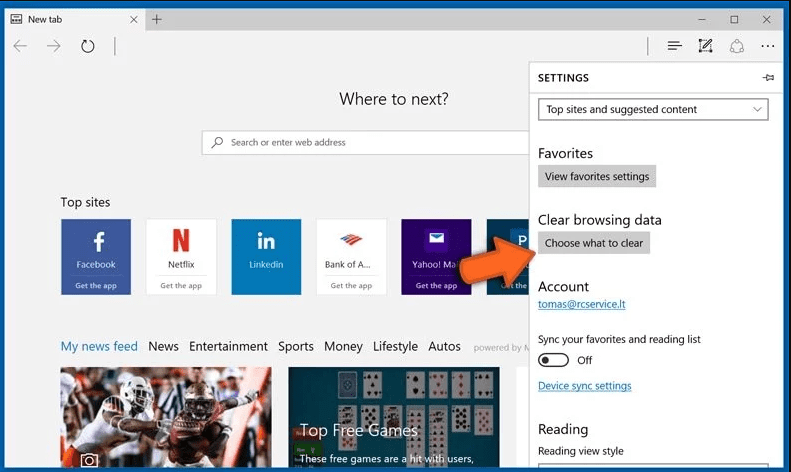
- Uninstall extensions from Microsoft Edge
Start the Microsoft Edge browser and go to the three horizontal dot icons at the top right corner of the browser. Choose all the recently installed extensions and right-click to find the “Uninstall” option. You can click on it to uninstall it.
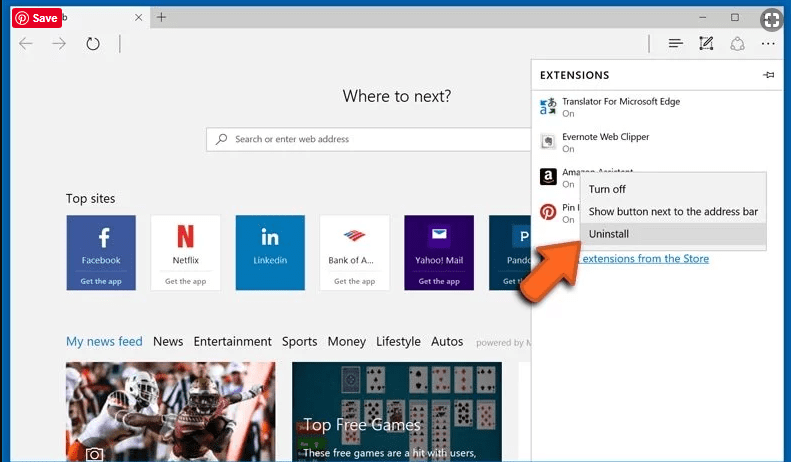
Another way to do it, if the issue continues, is:
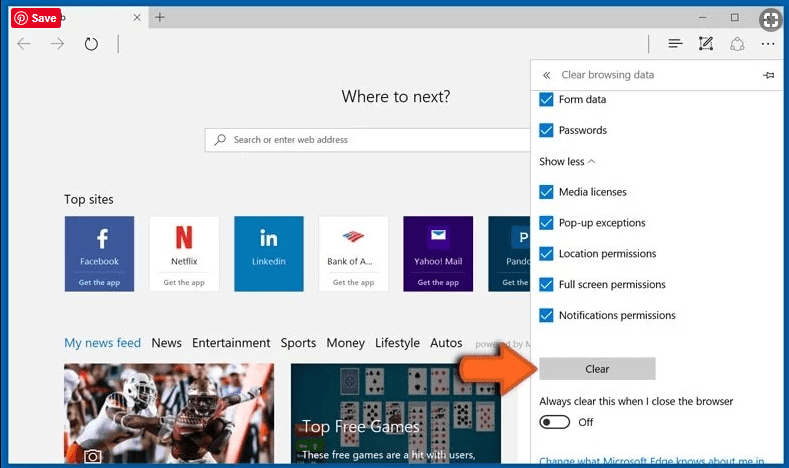
Go to the browser “Settings.”
Click on the “Choose what to clear” button.
Now click on “Show More” to select all the options before clicking on the “Clear” button.
Preventative tips for Counter.wmail-service.com Malware to enter your PC
- Instal Antivirus Software and turn on real-time scanning and automatic updates. It will help detect and block malware before they infect your PC.
- Keep the Software updated from your operating system to web browsers. Malware often exploits outdated Software.
- Browse Emails cautiously that are unsolicited and have attachments or links from unknown senders.
- Enable Firewall Protections to monitor and control incoming and outgoing network traffic.
- Download files and Software from trusted sources. Moreover, avoid downloading cracked Software, keygens, and other potentially malicious files from unreliable websites.
- Configure your browser to block pop-ups and disable automatic downloads and phishing.
- Avoid clicking on ads online that look suspicious and too good to be true.
- Disable the autorun process for external devices to prevent automatic wmail-service.com installation.
- Educate your team or network user to stay updated with the latest threats and practice safe online browsing.
- Make sure to regularly backup your important files to an external storage device or a secure cloud service. This way, you don’t have to fall for ransom demands.
Conclusion
Counter.wmail-service.com can be a dangerous harm like remote Access and control of infected systems and data theft. Preventative measures are important to protect against such threats. So keep up with the preventative tips mentioned above and follow through the blocking process to remove the malware. Take all these measures to reduce the risk of falling victim to Counter.wmail-service.com malware or other such threats.


